The ability of PC viruses to infect RAM, a computer’s temporary storage, is crucial to understand when discussing PC viruses.
A computer virus can infect RAM. Malicious code is loaded into RAM when a user runs an infected program. This infected program can manipulate and corrupt data and processes, jeopardizing the system’s integrity, performance, and other applications’ functionality.
RAM’s function as temporary storage for active applications and system processes is the main way viruses infect RAM. By infecting RAM, viruses can manipulate and corrupt running processes, spread further, carry out malicious operations, and frequently evade detection, leaving the system open to various dangers.
Other causes include using infected removable media, drive-by downloads, opening malicious email attachments, and exploiting software flaws. Each of these has the potential to insert viruses into RAM, having various negative effects on system performance and data security, which we will go into more detail about in the following sections.
Here are the reasons why a PC virus can infect RAM:
- Execution of Infected Programs
When a user launches a program containing a virus, the virus’s malicious code is loaded into the RAM, which can manipulate or corrupt temporary memory processes and data. - Exploitation of Software Vulnerabilities
By taking advantage of flaws in installed software, viruses can enter RAM and carry out malicious operations, endanger system stability, and possibly avoid detection by security programs. - Drive-by Downloads
Unintentional malicious software downloads can result in viruses living in RAM and compromising system security and performance. This typically happens when users unknowingly visit hacked or malicious websites. - Malicious Email Attachments
By loading viruses into RAM, which can disrupt system operations, steal sensitive data, and spread to other files and programs on the computer, opening infected email attachments can spread viruses that can harm other files and programs. - Infected Removable Media
By inserting infected USB drives or other removable media, you risk spreading viruses that take up RAM space, interfere with system performance, and affect other system components.
How to Fix RAM Infected By PC Virus?
Run a thorough system scan with up-to-date, dependable antivirus software to remove viruses with infected RAM. In addition to restoring the system’s integrity and performance, this procedure will find and remove the malicious code hiding in the RAM and stop the virus from harming your computer further.
The main techniques are installing powerful antivirus and antimalware tools, updating all software frequently, uninstalling dubious programs, and running security software. At the same time, it is in safe mode, which can further guarantee the eradication of any hidden threats. Regular automatic security scans are also essential to keep your computer system virus-free.
Additionally, taking preventative steps like using firewalls, avoiding dubious websites, not opening suspicious emails, and implementing network security can lessen the risk of infection. Additionally crucial are frequent backups, secure browsing, and user education regarding cybersecurity. We will delve deeper into each solution to offer a thorough overview of protecting RAM against viruses.
Here’s how you can fix RAM infected by PC virus:
1. Run Antivirus and Malware Removal Tools
2. Optimize Software and Operating Systems
3. Utilize Advanced Boot Options
4. Enhance System and Network Security
5. Adopt Safe Browsing and Email Practices
6. Maintain Data Integrity and Security
7. Seek Assistance and Education
Run Antivirus and Malware Removal Tools
It’s essential to install and frequently update antivirus and malware removal software. By scanning, identifying, and removing malicious software, these tools ensure the RAM and the entire system are secure. This proactive method is essential for keeping a computer healthy and safeguarding it from online threats.
Running these tools regularly offers continuous protection by spotting threats before they compromise the system. Users can ensure maximum security by automating scans and updates, preventing malicious software from residing in the RAM and jeopardizing the system’s functionality, stability, and data integrity.
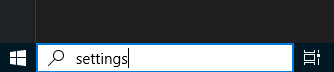
- Go to the Windows Search Bar and type “Settings.”
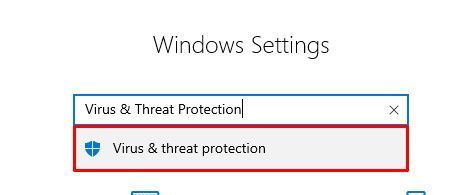
- Open the settings, and from the “Find a Setting” bar, type “Virus & Threat Protection.”
- On the right side of the screen, you will see an option “Open App.” Click on it.
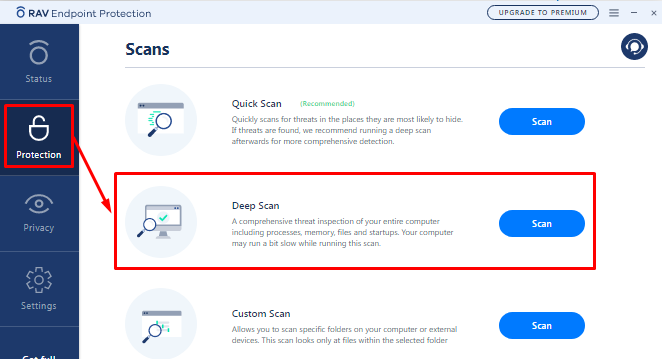
- After opening the antivirus software, go to the “Protection.”
- From the “Protection” tab, click on the “Deep Scan” to perform a full system scan.
Optimize Software and Operating Systems
Regular updates are crucial for operating system and software optimization. Updates frequently include security vulnerability patches to stop unauthorized access and potential RAM infections. By keeping the software up to date, you can protect your system from the most recent threats, enhance performance, and lower your risk of virus infection.
The process of system optimization also includes deleting any suspicious applications and files. Removing potential infection sources protects RAM and other components. A secure, effective, and resilient computing environment free of malicious intrusions requires routine maintenance and operating system and software optimization.
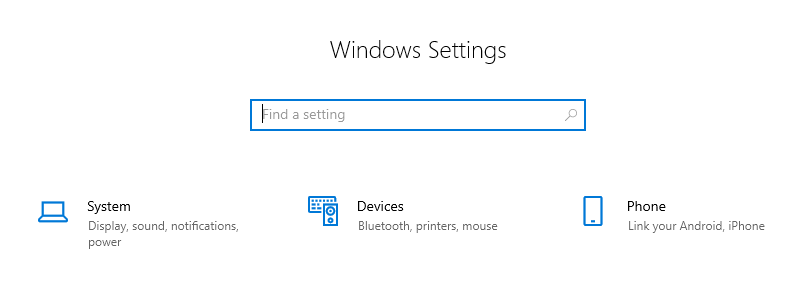
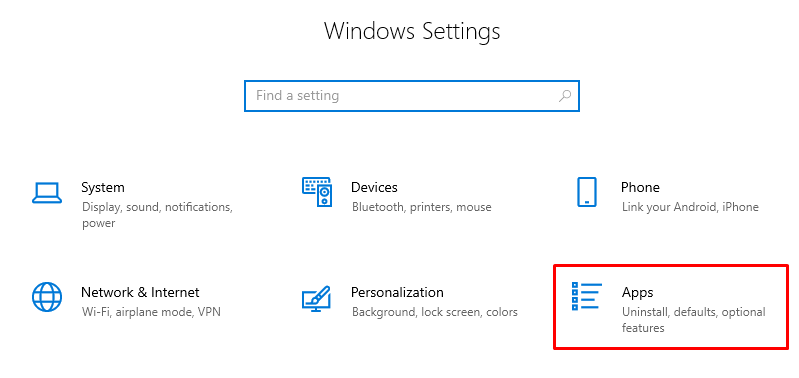
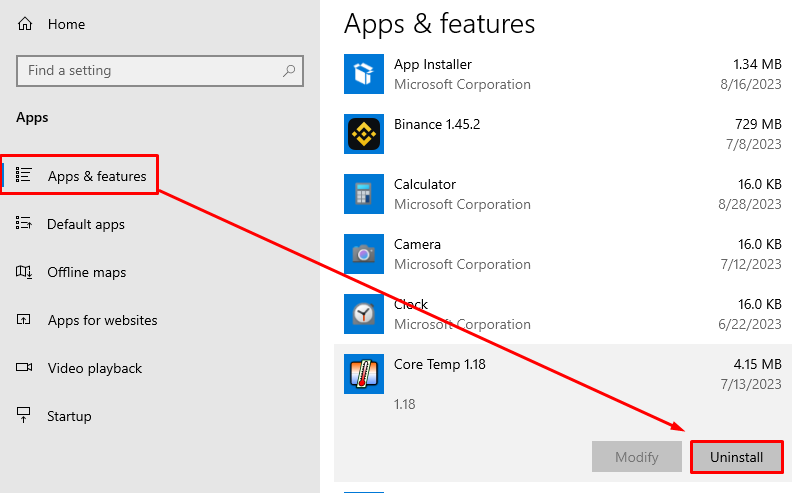
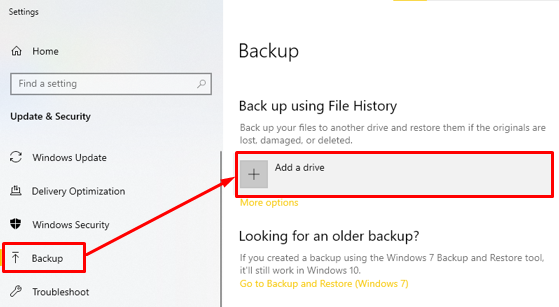
- First, you need to go to the “Settings.”
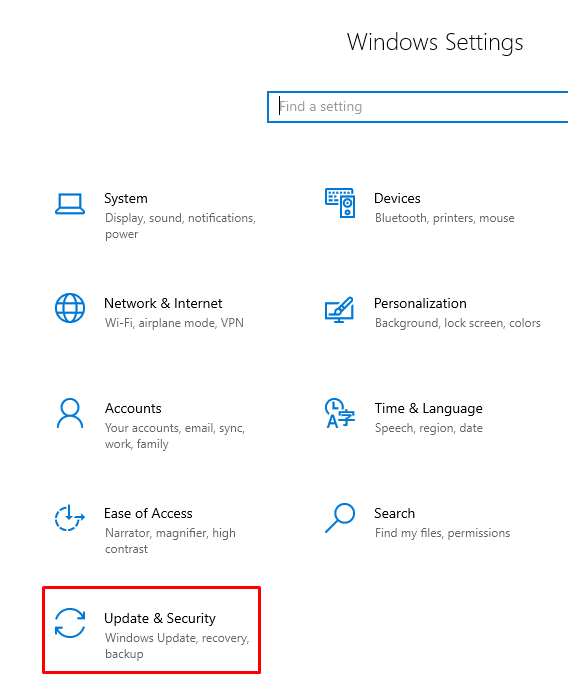
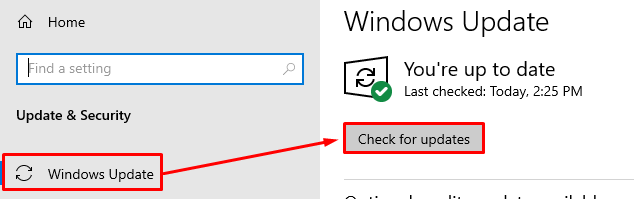
- After that, click on the “Update & Security” tab to open it.
- From there, open the “Windows Update” tab and check for any available updates.
- Return to the settings home page and navigate to “Apps.”
- From the “Apps” submenu, go to the “Apps & Features” tab. Review installed programs and uninstall any suspicious ones.
Utilize Advanced Boot Options
It is essential to use advanced boot options, such as Safe Mode. Users can effectively isolate and remove malicious software while operating in Safe Mode because only necessary programs are running. This method is especially helpful when dealing with viruses that are challenging to remove under standard operating conditions.
Reversing the changes made by malicious software by returning the system to a previous state can also be advantageous. This method can assist with data recovery and system stability by effectively undoing any changes the virus may have made to the RAM and other components of the system.
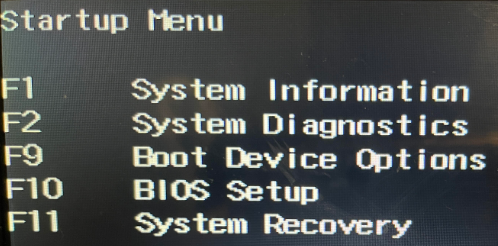
- Restart your computer. Press the designated key (usually F8) to access “Advanced Boot Options.”
- Select “Safe Mode” and press Enter. Run security software to remove threats.
Enhance System and Network Security
Implementing robust network security measures, such as firewalls, is crucial for enhancing system and network security. A formidable firewall acts as a barrier against unauthorized access, safeguarding the RAM from potential infections. By adopting comprehensive network security protocols, you can fortify the entire system network, minimize the risk of malicious intrusions, and establish a secure computing environment.
Encrypting Internet traffic and masking the IP address, a Virtual private network (VPN) enhances security measures. This ensures user privacy and safeguards the integrity of computer systems by preventing cyber criminals from intercepting sensitive information or injecting malicious software into RAM.
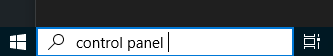
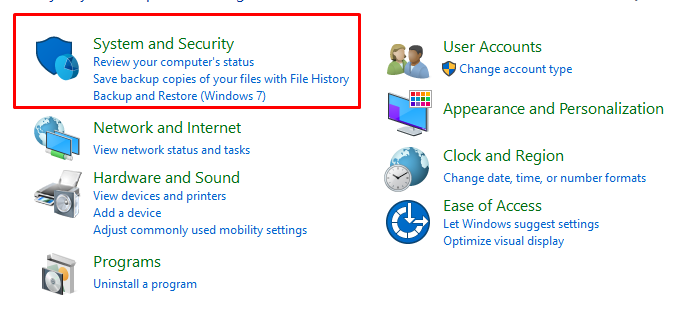
- Go to the “Windows Search Bar” and type “Control Panel.”
- From the “Control Panel” tab, navigate to “System and Security.”
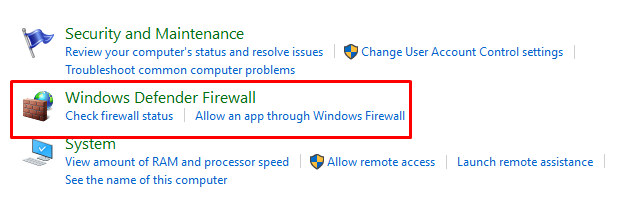
- Now, you need to open “Windows Defender Firewall.”
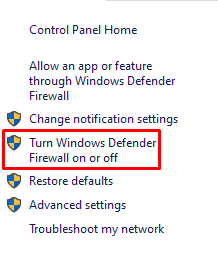
- Select “Turn Windows Defender Firewall on or off from the left side.“
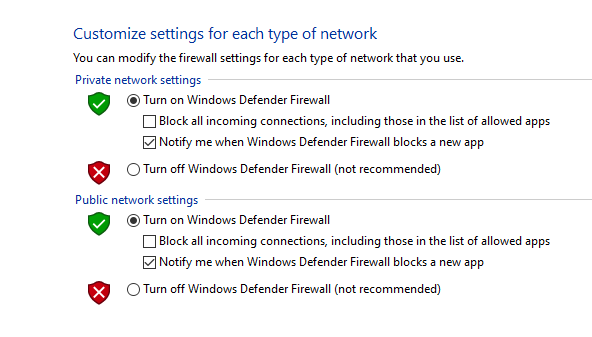
- Now, turn on the “Windows Defender Firewall.“
Adopt Safe Browsing and Email Practices
Practicing safe emailing and browsing habits is essential to prevent malicious RAM infiltrations. Users can significantly lower the risk of unintentionally downloading and running malicious software by avoiding untrusted websites and not opening suspicious emails or attachments, keeping their systems safe and operating at peak performance.
By implementing secure browsing techniques, such as using reliable and secure browsers and activating essential security features, the risk of RAM virus infections is further reduced. These practices ensure a protected online experience by blocking access to harmful websites and downloads, safeguarding your computer from potential threats and unauthorized usage.
Maintain Data Integrity and Security
To ensure data integrity, it is essential to regularly back up files and use passwords that are changed frequently. Backups prevent data loss caused by potential RAM infections, while strong passwords help prevent unauthorized access. By following these practices, you can safeguard private information and maintain the smooth functioning of computer systems.
Regularly monitoring system performance allows for early detection of irregularities or infections in the RAM, which enables prompt action to eliminate threats. Proactively monitoring and maintaining data integrity is crucial to prevent potential harm and ensure the reliability and durability of computer systems.
- Regularly backup important data to an external drive or cloud service.
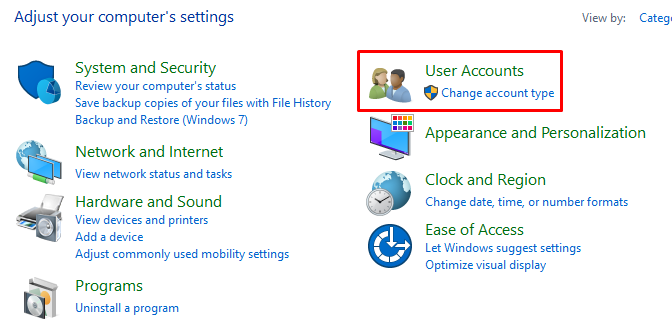
- Go to “Control Panel > User Accounts.”
- Change your password to update passwords regularly.
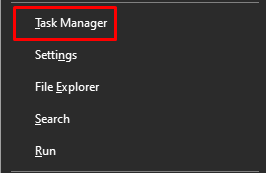
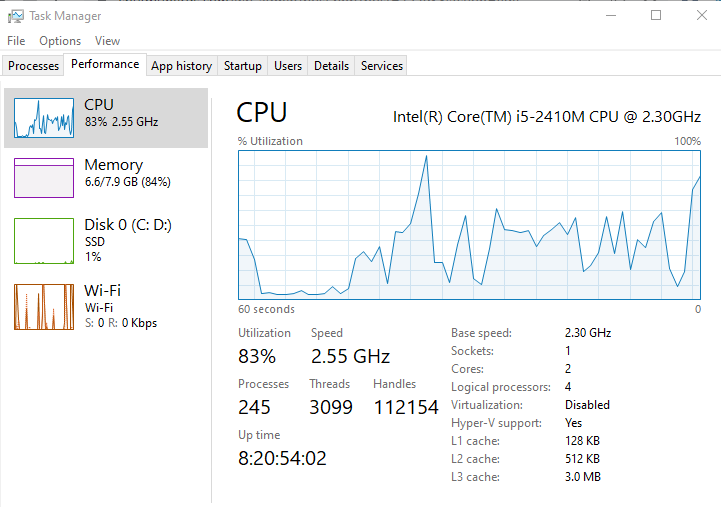
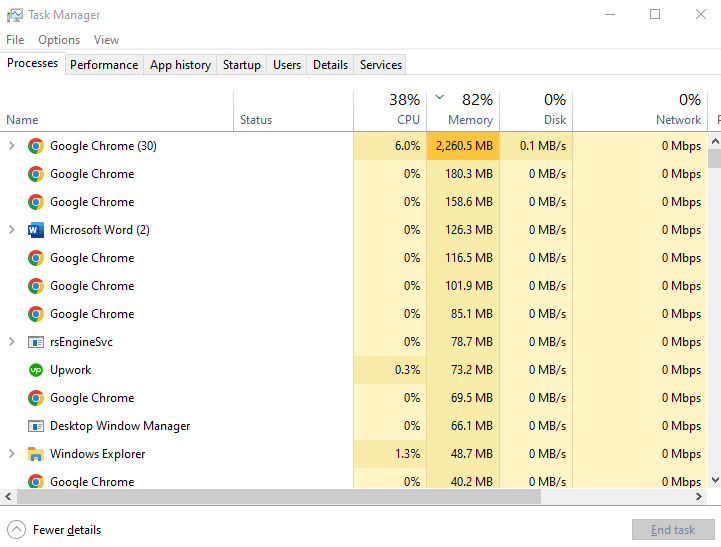
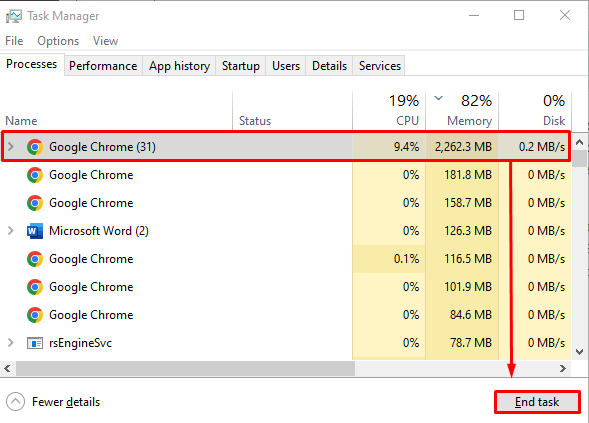
- After that, navigate to “Task Manager” by pressing the “Windows + X” keys.
- Monitor system performance and storage usage for abnormalities.
Seek Assistance and Education
To prevent RAM infections, seeking professional technical assistance and educate users on best cybersecurity practices is crucial. Expert help can provide tailored solutions while informed users are less vulnerable to malicious attacks, ensuring overall system security and optimal performance.
Having knowledgeable users who can identify and avoid potential threats is key to reducing the risk of viruses infecting computer memory. Regular training and raising awareness among users helps them to detect suspicious activities and take appropriate actions, safeguarding systems against malware and preventing the compromise of sensitive information.
Manage System Resources
To keep your computer system running smoothly, managing its resources is important. This includes regularly deleting temporary files and clearing up RAM. By eliminating unnecessary data, you can prevent the accumulation of malicious code in your computer’s memory. This not only boosts system performance but also reduces the risk of virus infections.
By efficiently utilizing system resources, computers can become less vulnerable to infections and operate smoothly. Users can avoid slowdowns and crashes by regularly cleaning and optimizing their RAM. This prolongs the lifespan of hardware components and enhances the overall user experience.
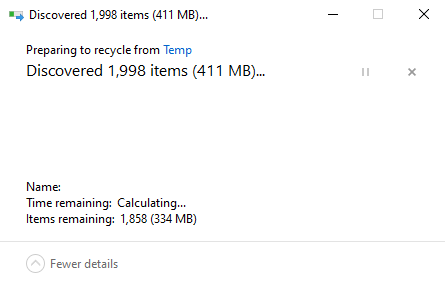
- Press “Ctrl + Shift + Esc” to open “Task Manager.”
- End unnecessary processes to clear RAM.
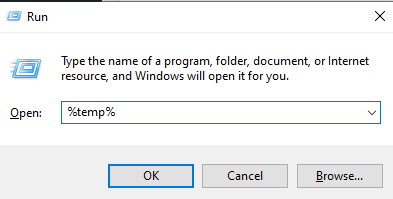
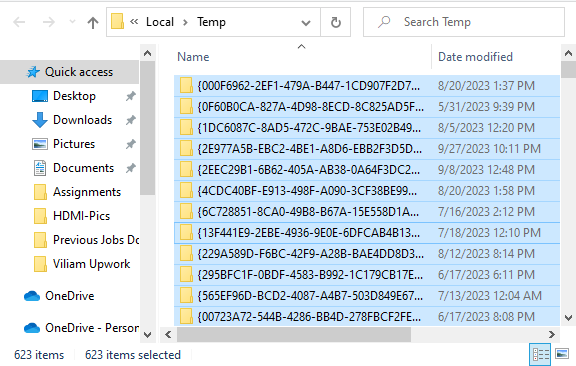
- Use the Disk Cleanup tool by pressing “Win” + “R.” Enter “%temp%” as a prompt and then press enter.
- Press “Ctrl” + “A” to select all the temporary files.
- Pressing “Ctrl” + “D” to delete. Remove temporary files by pressing enter.
Conclusion
It is essential to comprehend how viruses enter and function within computer systems. These malicious actors are skilled at finding flaws, running malicious code, and spreading throughout files and networks. They highlight the need for strong cybersecurity measures and regular best practices.
Because they can seriously degrade system performance, compromise data integrity, and introduce security holes, employing dependable security software and updating systems are essential to fend off these threats. Regular software patches and updates strengthen system defenses by addressing vulnerabilities that viruses could exploit. Additionally, it’s crucial to use safe browsing techniques, be cautious when opening emails, and regularly back up your data to reduce the risk of virus infections.
To stop further damage, it is necessary to recognize the symptoms of virus infections. Elevated memory usage, unexpected system behavior, and frequent crashes indicate possible infections. Prompt and appropriate responses, such as running system scans and uninstalling suspicious programs, are essential to restore system stability and security.
In conclusion, securing computer systems against viruses requires a thorough strategy that includes precautions, frequent updates, user vigilance, and quick reaction to symptoms. In the face of evolving cyber threats, this multifaceted strategy guarantees data security and upholds optimal system performance.

Hey, I’m Hammad. I write for this website to help you with the IT advice about PC, RAM, CPU, Motherboard, PSU, and other PC components.
I will provide detailed guides with images, and explain step by step so you can understand the process. Check all my articles here.